NetworkManager.confNetworkManager.conf — NetworkManager configuration file |
Synopsis
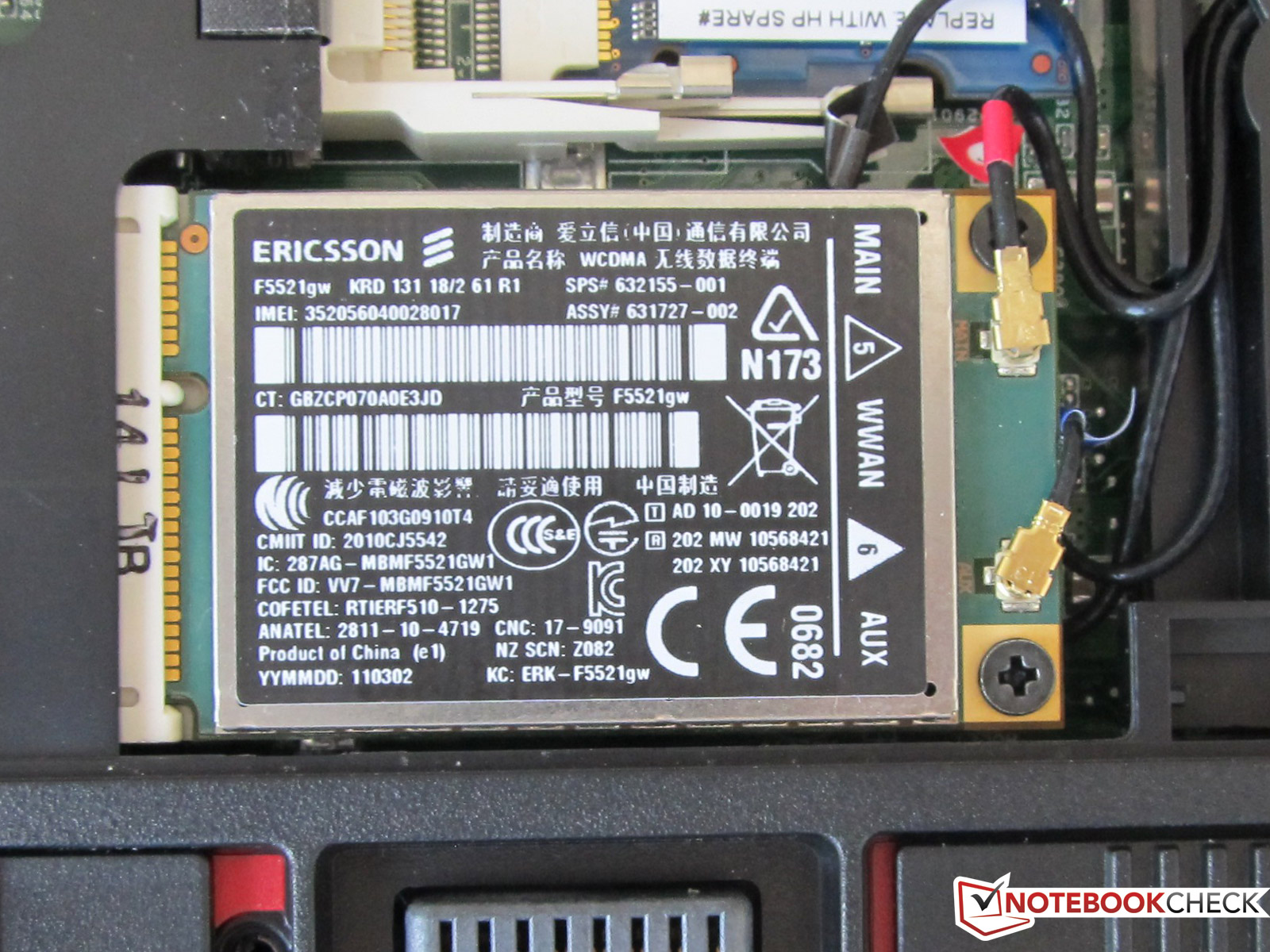
Software Update 2 for WEH WWAN Firmware ver. 2.11: 926Kb: This software update improves performance of the device by addressing issues found since the last major operating system release. Adds compliance with ETSI EN300 version 3.2.8. It is recommended that this software update be installed on all production CN51 WEH v2.11 WWAN units. Apple WWAN Support Update 1.0 Released Posted by Andru Edwards Categories: Apple, Broadband, PC / Laptop, Software, Wireless / WiFi, USB As I was Twittering, Software Update popped up and notified me that there is a WWAN Support Update available.
/etc/NetworkManager/NetworkManager.conf, /etc/NetworkManager/conf.d/, name.conf/run/NetworkManager/conf.d/, name.conf/usr/lib/NetworkManager/conf.d/, name.conf/var/lib/NetworkManager/NetworkManager-intern.conf
Description
NetworkManager.conf is the configuration file for NetworkManager. It is used to set up various aspects of NetworkManager's behavior. The location of the main file and configuration directories may be changed through use of the --config, --config-dir, --system-config-dir, and --intern-config argument for NetworkManager, respectively.
If a default NetworkManager.conf is provided by your distribution's packages, you should not modify it, since your changes may get overwritten by package updates. Instead, you can add additional .conf files to the /etc/NetworkManager/conf.d directory. These will be read in order, with later files overriding earlier ones. Packages might install further configuration snippets to /usr/lib/NetworkManager/conf.d. This directory is parsed first, even before NetworkManager.conf. Scripts can also put per-boot configuration into /run/NetworkManager/conf.d. This directory is parsed second, also before NetworkManager.conf. The loading of a file /run/NetworkManager/conf.d/ can be prevented by adding a file name.conf/etc/NetworkManager/conf.d/. Likewise, a file name.conf/usr/lib/NetworkManager/conf.d/ can be shadowed by putting a file of the same name to either name.conf/etc/NetworkManager/conf.d or /run/NetworkManager/conf.d.
NetworkManager can overwrite certain user configuration options via D-Bus or other internal operations. In this case it writes those changes to /var/lib/NetworkManager/NetworkManager-intern.conf. This file is not intended to be modified by the user, but it is read last and can shadow user configuration from NetworkManager.conf.
Certain settings from the configuration can be reloaded at runtime either by sending SIGHUP signal or via D-Bus' Reload call.
File Format
The configuration file format is so-called key file (sort of ini-style format). It consists of sections (groups) of key-value pairs. Lines beginning with a '#' and blank lines are considered comments. Sections are started by a header line containing the section enclosed in '[' and ']', and ended implicitly by the start of the next section or the end of the file. Each key-value pair must be contained in a section.
For keys that take a list of devices as their value, you can specify devices by their MAC addresses or interface names, or '*' to specify all devices. See the section called “Device List Format” below.
Minimal system settings configuration file looks like this:
As an extension to the normal keyfile format, you can also append a value to a previously-set list-valued key by doing:
main section
| Lists system settings plugin names separated by ','. These plugins are used to read and write system-wide connection profiles. When multiple plugins are specified, the connections are read from all listed plugins. When writing connections, the plugins will be asked to save the connection in the order listed here; if the first plugin cannot write out that connection type (or can't write out any connections) the next plugin is tried, etc. If none of the plugins can save the connection, an error is returned to the user. The default value and the number of available plugins is distro-specific. See the section called “Plugins” below for the available plugins. Note that NetworkManager's native |
| This setting is deprecated and has no effect. Profiles from disk are never automatically reloaded. Use for example |
| Whether the system uses PolicyKit for authorization. If |
| This key sets up what DHCP client NetworkManager will use. Allowed values are If this key is missing, it defaults to |
| Specify devices for which NetworkManager shouldn't create default wired connection (Auto eth0). By default, NetworkManager creates a temporary wired connection for any Ethernet device that is managed and doesn't have a connection configured. List a device in this option to inhibit creating the default connection for the device. May have the special value When the default wired connection is deleted or saved to a new persistent connection by a plugin, the device is added to a list in the file See the section called “Device List Format” for the syntax how to specify a device. Example: |
| This setting is deprecated for the per-device setting |
| Specify devices for which NetworkManager will try to generate a connection based on initial configuration when the device only has an IPv6 link-local address. See the section called “Device List Format” for the syntax how to specify a device. |
| When set to ' |
| Set the management mode of the hostname. This parameter will affect only the transient hostname. If a valid static hostname is set, NetworkManager will skip the update of the hostname despite the value of this option. An hostname empty or equal to 'localhost', 'localhost6', 'localhost.localdomain' or 'localhost6.localdomain' is considered invalid.
|
| Set the DNS processing mode. If the key is unspecified,
Note that the plugins When using |
| Set the If you configure
|
| Send the connection DNS configuration to Note that this setting is complementary to the If systemd-resolved is enabled, the connectivity check resolves the hostname per-device. |
| Comma separated list of options to aid debugging. This value will be combined with the environment variable
|
| The number of times a connection activation should be automatically tried before switching to another one. This value applies only to connections that can auto-connect and have a |
| This key specifies in which order slave connections are auto-activated on boot or when the master activates them. Allowed values are |
keyfile section
This section contains keyfile-plugin-specific options, and is normally only used when you are not using any other distro-specific plugin.
| This key is deprecated and has no effect since the hostname is now stored in |
| The location where keyfiles are read and stored. This defaults to ' |
| Set devices that should be ignored by NetworkManager. See the section called “Device List Format” for the syntax on how to specify a device. Example: |
ifupdown section
This section contains ifupdown-specific options and thus only has effect when using the ifupdown plugin.
| If set to The default value is |
logging section
This section controls NetworkManager's logging. Any settings here are overridden by the --log-level and --log-domains command-line options.
| The default logging verbosity level. One of |
| The following log domains are available: PLATFORM, RFKILL, ETHER, WIFI, BT, MB, DHCP4, DHCP6, PPP, WIFI_SCAN, IP4, IP6, AUTOIP4, DNS, VPN, SHARING, SUPPLICANT, AGENTS, SETTINGS, SUSPEND, CORE, DEVICE, OLPC, WIMAX, INFINIBAND, FIREWALL, ADSL, BOND, VLAN, BRIDGE, DBUS_PROPS, TEAM, CONCHECK, DCB, DISPATCH, AUDIT, SYSTEMD, VPN_PLUGIN, PROXY. In addition, these special domains can be used: NONE, ALL, DEFAULT, DHCP, IP. You can specify per-domain log level overrides by adding a colon and a log level to any domain. E.g., ' |
| The logging backend. Supported values are ' |
| Whether the audit records are delivered to auditd, the audit daemon. If |
connection section
Specify default values for connections.
Example:
Supported Properties
Not all properties can be overwritten, only the following properties are supported to have their default values configured (see nm-settings(5) for details). A default value is only consulted if the corresponding per-connection value explicitly allows for that.
| |
| |
| If left unspecified, the default value is 3 tries before failing the connection. |
| |
| If unspecified, MUD URL defaults to |
| |
| If unspecified, the ultimate default values depends on the DNS plugin. With systemd-resolved the default currently is 'yes' (2) and for all other plugins 'no' (0). |
| If unspecified, the ultimate default values depends on the DNS plugin. With systemd-resolved the default currently is 'no' (0) and for all other plugins also 'no' (0). |
| |
| If left unspecified, it defaults to 'preserve'. |
| |
| If configured explicitly to 0, the MTU is not reconfigured during device activation unless it is required due to IPv6 constraints. If left unspecified, a DHCP/IPv6 SLAAC provided value is used or the MTU is not reconfigured during activation. |
| |
| |
| If configured explicitly to 0, the MTU is not reconfigured during device activation unless it is required due to IPv6 constraints. If left unspecified, a DHCP/IPv6 SLAAC provided value is used or the MTU is left unspecified on activation. |
| If configured explicitly to 0, the MTU is not reconfigured during device activation unless it is required due to IPv6 constraints. If left unspecified, a DHCP/IPv6 SLAAC provided value is used or a default of 1500. |
| |
| |
| If left unspecified, it defaults to 'ifname'. |
| If left unspecified, the value 3 (fqdn-encoded,fqdn-serv-update) is used. |
| If left unspecified, the default value for the interface type is used. |
| If left unspecified, the default is to not send the DHCP option to the server. |
| If unspecified or zero, use 50 for VPN profiles and 100 for other profiles. |
| |
| If left unspecified, routes are only added to the main table. Note that this is different from explicitly selecting the main table 254, because of how NetworkManager removes extraneous routes from the tables. |
| If left unspecified, the default value depends on the sysctl solicitation settings. |
| If left unspecified, it defaults to 'lease'. |
| If left unspecified, it defaults to 'ifname'. |
| If left unspecified, the value 1 (fqdn-serv-update) is used. |
| If left unspecified, the default value for the interface type is used. |
| If unspecified or zero, use 50 for VPN profiles and 100 for other profiles. |
| If |
| |
| If left unspecified, routes are only added to the main table. Note that this is different from explicitly selecting the main table 254, because of how NetworkManager removes extraneous routes from the tables. |
| If left unspecified, drivers are autoprobed when the SR-IOV VF gets created. |
| If left unspecified, default value of 60 seconds is used. |
| If left unspecified, AP isolation is disabled. |
| If left unspecified, it defaults to 'preserve'. |
| |
| If left unspecified, MAC address randomization is disabled. This setting is deprecated for |
| If configured explicitly to 0, the MTU is not reconfigured during device activation unless it is required due to IPv6 constraints. If left unspecified, a DHCP/IPv6 SLAAC provided value is used or a default of 1500. |
| If left unspecified, the default value ' |
| If left unspecified, the default value ' |
| If left unspecified, the default value ' |
| |
|
Sections
You can configure multiple connection sections, by having different sections with a name that all start with 'connection'. Example:
The sections within one file are considered in order of appearance, with the exception that the [connection] section is always considered last. In the example above, this order is [connection-wifi-wlan0], [connection-wlan-other], and [connection]. When checking for a default configuration value, the sections are searched until the requested value is found. In the example above, 'ipv4.route-metric' for wlan0 interface is set to 50, and for all other Wi-Fi typed interfaces to 55. Also, Wi-Fi devices would have IPv6 private addresses enabled by default, but other devices would have it disabled. Note that also 'wlan0' gets 'ipv6.ip6-privacy=1', because although the section '[connection-wifi-wlan0]' matches the device, it does not contain that property and the search continues.
When having different sections in multiple files, sections from files that are read later have higher priority. So within one file the priority of the sections is top-to-bottom. Across multiple files later definitions take precedence.
The following properties further control how a connection section applies.
| An optional device spec that restricts when the section applies. See the section called “Device List Format” for the possible values. |
| An optional boolean value which defaults to |
device section
Contains per-device persistent configuration.
Example:
Supported Properties
The following properties can be configured per-device.
| Whether the device is managed or not. A device can be marked as managed via udev rules (ENV{NM_UNMANAGED}), or via setting plugins (keyfile.unmanaged-devices). This is yet another way. Note that this configuration can be overruled at runtime via D-Bus. Also, it has higher priority then udev rules. |
| Specify the timeout for waiting for carrier in milliseconds. When the device loses carrier, NetworkManager does not react immediately. Instead, it waits for this timeout before considering the link lost. Also, on startup, NetworkManager considers the device as busy for this time, as long as the device has no carrier. This delays startup-complete signal and NetworkManager-wait-online. Configuring this too high means to block NetworkManager-wait-online longer then necessary. Configuring it too low, means that NetworkManager will declare startup-complete, although carrier is about to come and auto-activation to kick in. The default is 5000 milliseconds. |
| Specify devices for which NetworkManager will (partially) ignore the carrier state. Normally, for device types that support carrier-detect, such as Ethernet and InfiniBand, NetworkManager will only allow a connection to be activated on the device if carrier is present (ie, a cable is plugged in), and it will deactivate the device if carrier drops for more than a few seconds. A device with carrier ignored will allow activating connections on that device even when it does not have carrier, provided that the connection uses only statically-configured IP addresses. Additionally, it will allow any active connection (whether static or dynamic) to remain active on the device when carrier is lost. Note that the 'carrier' property of NMDevices and device D-Bus interfaces will still reflect the actual device state; it's just that NetworkManager will not make use of that information. Master types like bond, bridge and team ignore carrier by default, while other device types react on carrier changes by default. This setting overwrites the deprecated |
| Configures MAC address randomization of a Wi-Fi device during scanning. This defaults to |
| Specify the Wi-Fi backend used for the device. Currently, supported are |
| Like the per-connection settings |
| Specify the number of virtual functions (VF) to enable for a PCI physical device that supports single-root I/O virtualization (SR-IOV). |
Sections
The [device] section works the same as the [connection] section. That is, multiple sections that all start with the prefix 'device' can be specified. The settings 'match-device' and 'stop-match' are available to match a device section on a device. The order of multiple sections is also top-down within the file and later files overwrite previous settings. See “Sections” under the section called “CONNECTION SECTION” for details.
connectivity section
This section controls NetworkManager's optional connectivity checking functionality. This allows NetworkManager to detect whether or not the system can actually access the internet or whether it is behind a captive portal.
Connectivity checking serves two purposes. For one, it exposes a connectivity state on D-Bus, which other applications may use. For example, Gnome's portal helper uses this as signal to show a captive portal login page. The other use is that default-route of devices without global connectivity get a penalty of +20000 to the route-metric. This has the purpose to give a better default-route to devices that have global connectivity. For example, when being connected to WWAN and to a Wi-Fi network which is behind a captive portal, WWAN still gets preferred until login.
Note that your distribution might set /proc/sys/net/ipv4/conf/*/rp_filter to strict filtering. That works badly with per-device connectivity checking, which uses SO_BINDDEVICE to send requests on all devices. A strict rp_filter setting will reject any response and the connectivity check on all but the best route will fail.
| Whether connectivity check is enabled. Note that to enable connectivity check, a valid uri must also be configured. The value defaults to true, but since the uri is unset by default, connectivity check may be disabled. The main purpose of this option is to have a single flag to disable connectivity check. Note that this setting can also be set via D-Bus API at runtime. In that case, the value gets stored in |
| The URI of a web page to periodically request when connectivity is being checked. This page should return the header 'X-NetworkManager-Status' with a value of 'online'. Alternatively, its body content should be set to 'NetworkManager is online'. The body content check can be controlled by the |
| Specified in seconds; controls how often connectivity is checked when a network connection exists. If set to 0 connectivity checking is disabled. If missing, the default is 300 seconds. |
| If set, controls what body content NetworkManager checks for when requesting the URI for connectivity checking. Note that this only compares that the HTTP response starts with the specifid text, it does not compare the exact string. This behavior might change in the future, so avoid relying on it. If missing, the response defaults to 'NetworkManager is online'. If set to empty, the HTTP server is expected to answer with status code 204 or send no data. |
global-dns section

This section specifies global DNS settings that override connection-specific configuration.
| A list of search domains to be used during hostname lookup. |
| A list of options to be passed to the hostname resolver. |
global-dns-domain sections
Sections with a name starting with the 'global-dns-domain-' prefix allow to define global DNS configuration for specific domains. The part of section name after 'global-dns-domain-' specifies the domain name a section applies to. More specific domains have the precedence over less specific ones and the default domain is represented by the wildcard '*'. A default domain section is mandatory.
| A list of addresses of DNS servers to be used for the given domain. |
| A list of domain-specific DNS options. Not used at the moment. |
.config sections
This is a special section that contains options which apply to the configuration file that contains the option.
| Defaults to ' You can also match against the version of NetworkManager. For example the following are valid configurations: You can also match against the value of the environment variable More then one match can be specified. The configuration will be enabled if one of the predicates matches ('or'). The special prefix 'except:' can be used to negate the match. Note that if one except-predicate matches, the entire configuration will be disabled. In other words, a except predicate always wins over other predicates. If the setting only consists of 'except:' matches and none of the negative conditions are satisfied, the configuration is still enabled. |
Plugins
Settings plugins for reading and writing connection profiles. The number of available plugins is distribution specific.
| The The stored connection file may contain passwords, secrets and private keys in plain text, so it will be made readable only to root, and the plugin will ignore files that are readable or writable by any user or group other than root. See 'Secret flag types' in nm-settings(5) for how to avoid storing passwords in plain text. This plugin is always active, and will automatically be used to store any connections that aren't supported by any other active plugin. |
| This plugin is used on the Fedora and Red Hat Enterprise Linux distributions to read and write configuration from the standard |
| This plugin is used on the Debian and Ubuntu distributions, and reads Ethernet and Wi-Fi connections from This plugin is read-only; any connections (of any type) added from within NetworkManager when you are using this plugin will be saved using the |
| These plugins are deprecated and their selection has no effect. This is now handled by nm-initrd-generator. |
| These plugins are deprecated and their selection has no effect. The |
Wwan Support Update 1.0 (for Mac) Hp
Appendix
Device List Format
The configuration options main.no-auto-default, main.ignore-carrier, keyfile.unmanaged-devices, connection*.match-device and device*.match-device select devices based on a list of matchings. Devices can be specified using the following format:
* | Matches every device. |
IFNAME | Case sensitive match of interface name of the device. Globbing is not supported. |
HWADDR | Match the permanent MAC address of the device. Globbing is not supported |
interface-name:IFNAME, interface-name:~IFNAME | Case sensitive match of interface name of the device. Simple globbing is supported with |
interface-name:=IFNAME | Case sensitive match of interface name of the device. Globbing is disabled and |
mac:HWADDR | Match the permanent MAC address of the device. Globbing is not supported |
s390-subchannels:HWADDR | Match the device based on the subchannel address. Globbing is not supported |
type:TYPE | Match the device type. Valid type names are as reported by ' |
driver:DRIVER | Match the device driver as reported by ' |
dhcp-plugin:DHCP | Match the configured DHCP plugin ' |
except:SPEC | Negative match of a device. If there is a list consisting only of negative matches, the behavior is the same as if there is also match-all. That means, if none of all the negative matches is satisfied, the overall result is still a positive match. That means, |
SPEC[,;]SPEC | Multiple specs can be concatenated with commas or semicolons. The order does not matter as matches are either inclusive or negative ( Backslash is supported to escape the separators ';' and ',', and to express special characters such as newline ('n'), tabulator ('t'), whitespace ('s') and backslash ('). The globbing of interface names cannot be escaped. Whitespace is not a separator but will be trimmed between two specs (unless escaped as 's'). |
Example:
Wwan Support Update 1.0 (for Mac) Laptop
See Also
Wwan Support Update 1.0 (for Mac) Windows 10
NetworkManager(8), nmcli(1), nmcli-examples(7), nm-online(1), nm-settings(5), nm-applet(1), nm-connection-editor(1)